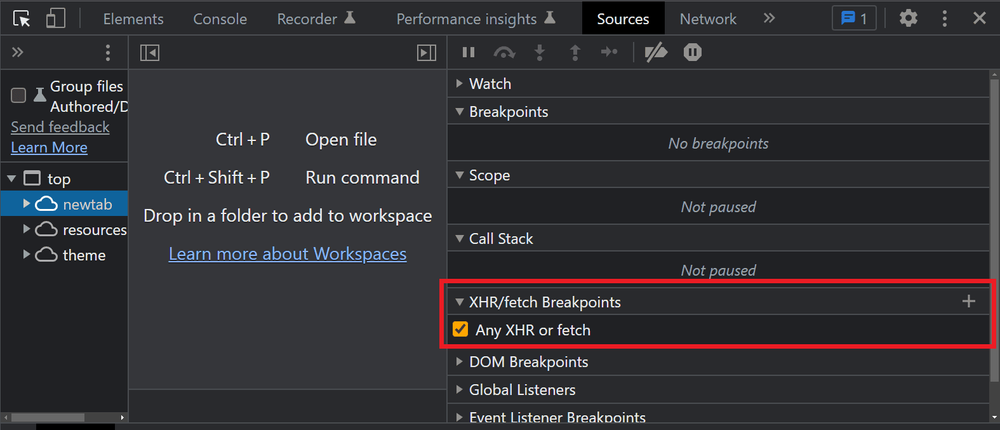
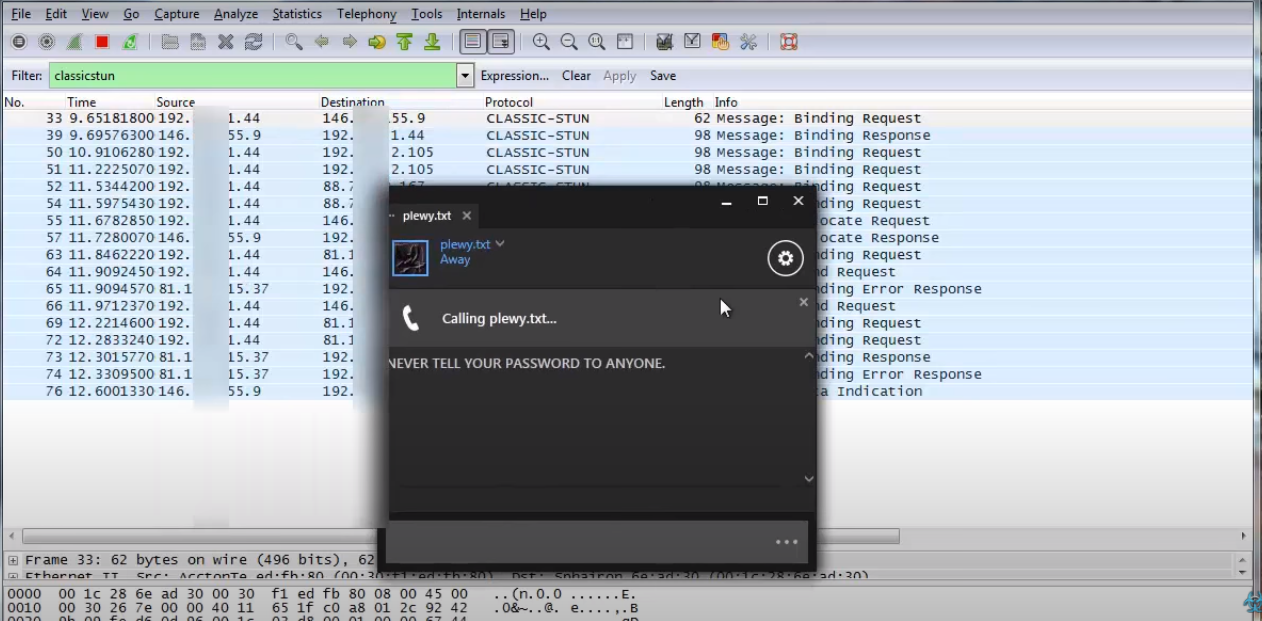
Credential Stuffing 2.0: The Use of Proxies, CAPTCHA Bypassing
Por um escritor misterioso
Last updated 09 novembro 2024
Welcome to the new age of cyber attacks, where hackers have taken credential stuffing to the next level. Meet Credential Stuffing 2.0, where the use of proxies, CAPTCHA bypassing, CloudFlare security, and GUI tools have become the norm..
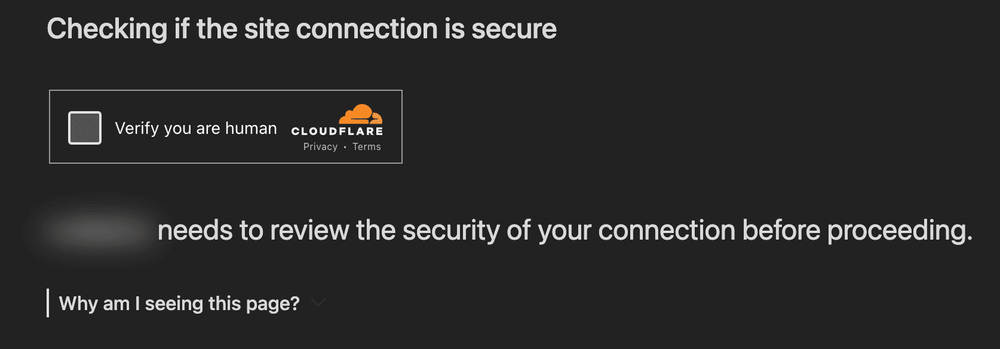
How to Bypass Cloudflare in 2023: The 8 Best Methods - ZenRows
How to Prevent Credential Stuffing
The Anatomy of Highly Profitable Credential Stuffing Attacks

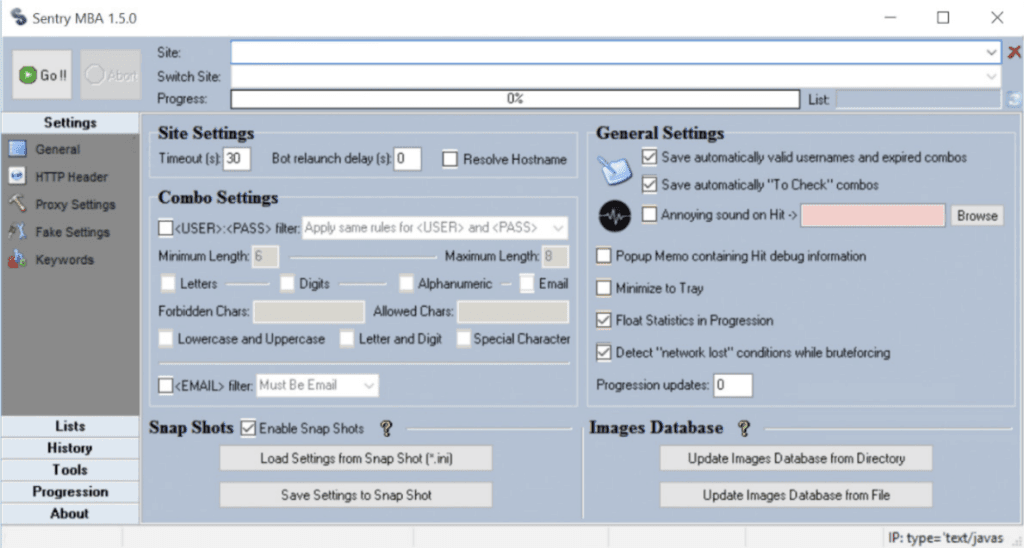
How OpenBullet is used to attack websites, and how to block it.
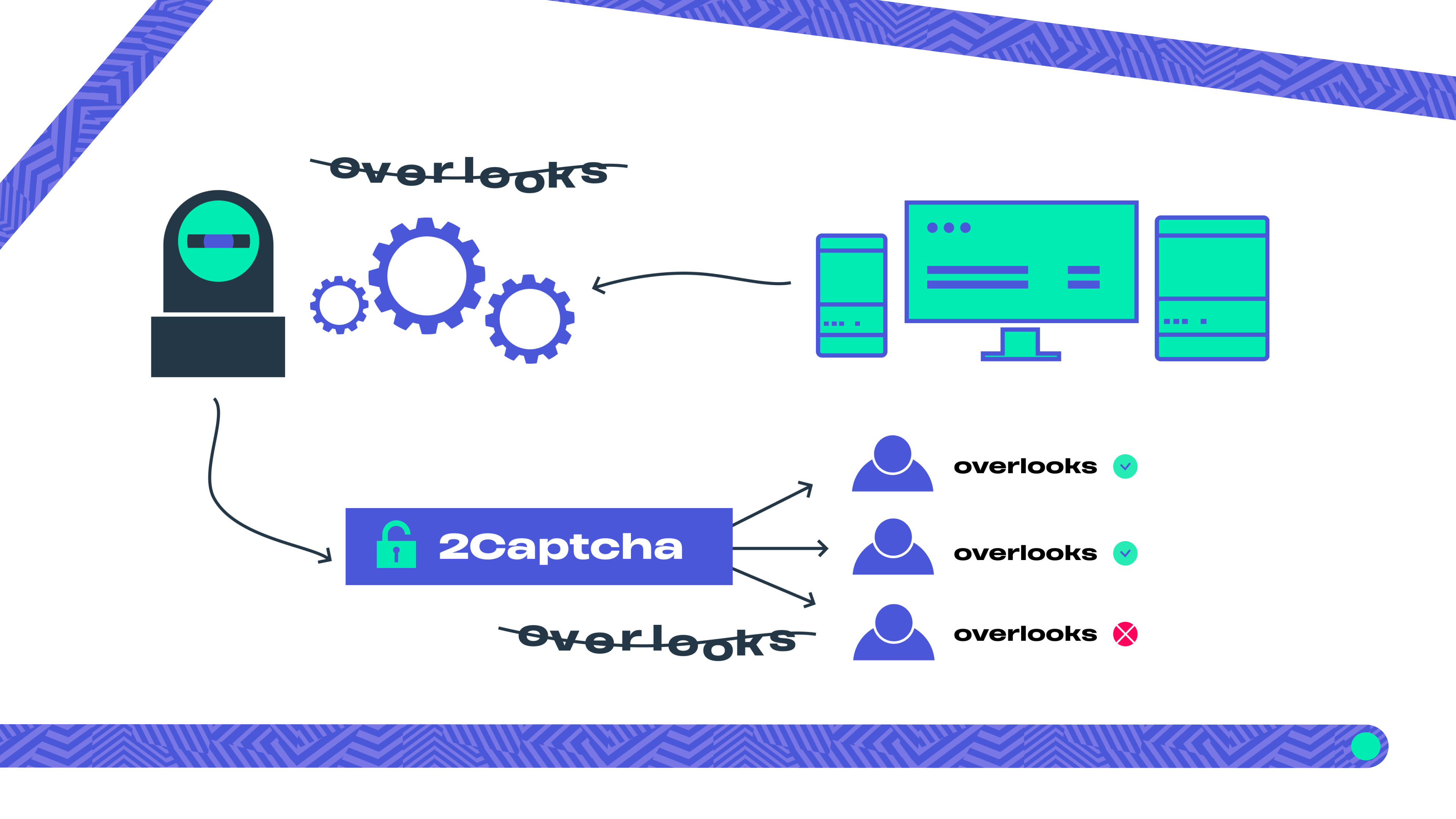
What Are CAPTCHA Proxies and How Do They Work?
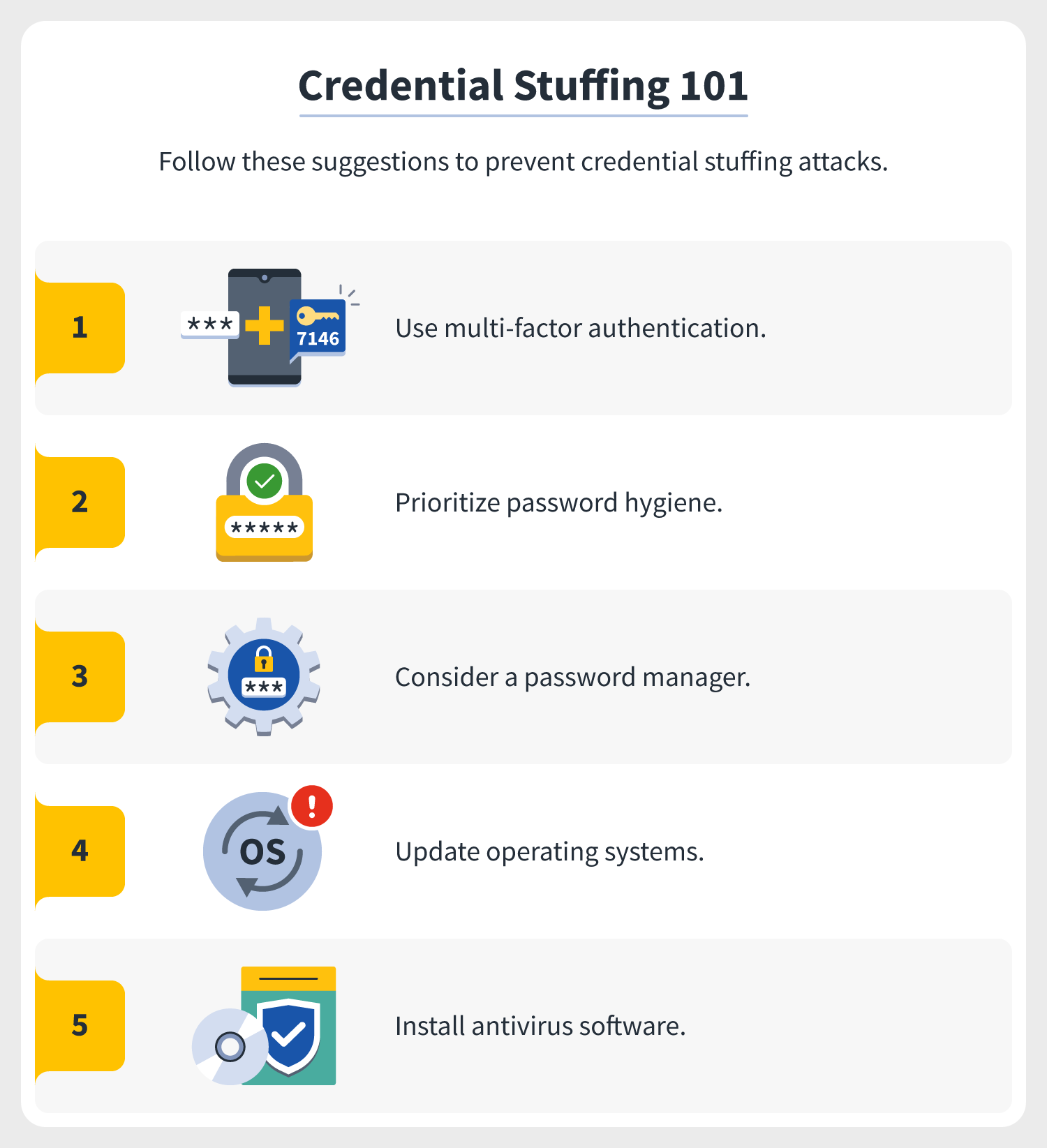
Credential stuffing simplified + attack protection tips

ReCAPTCHA Alternative: How to Stop Bad Bots For Good
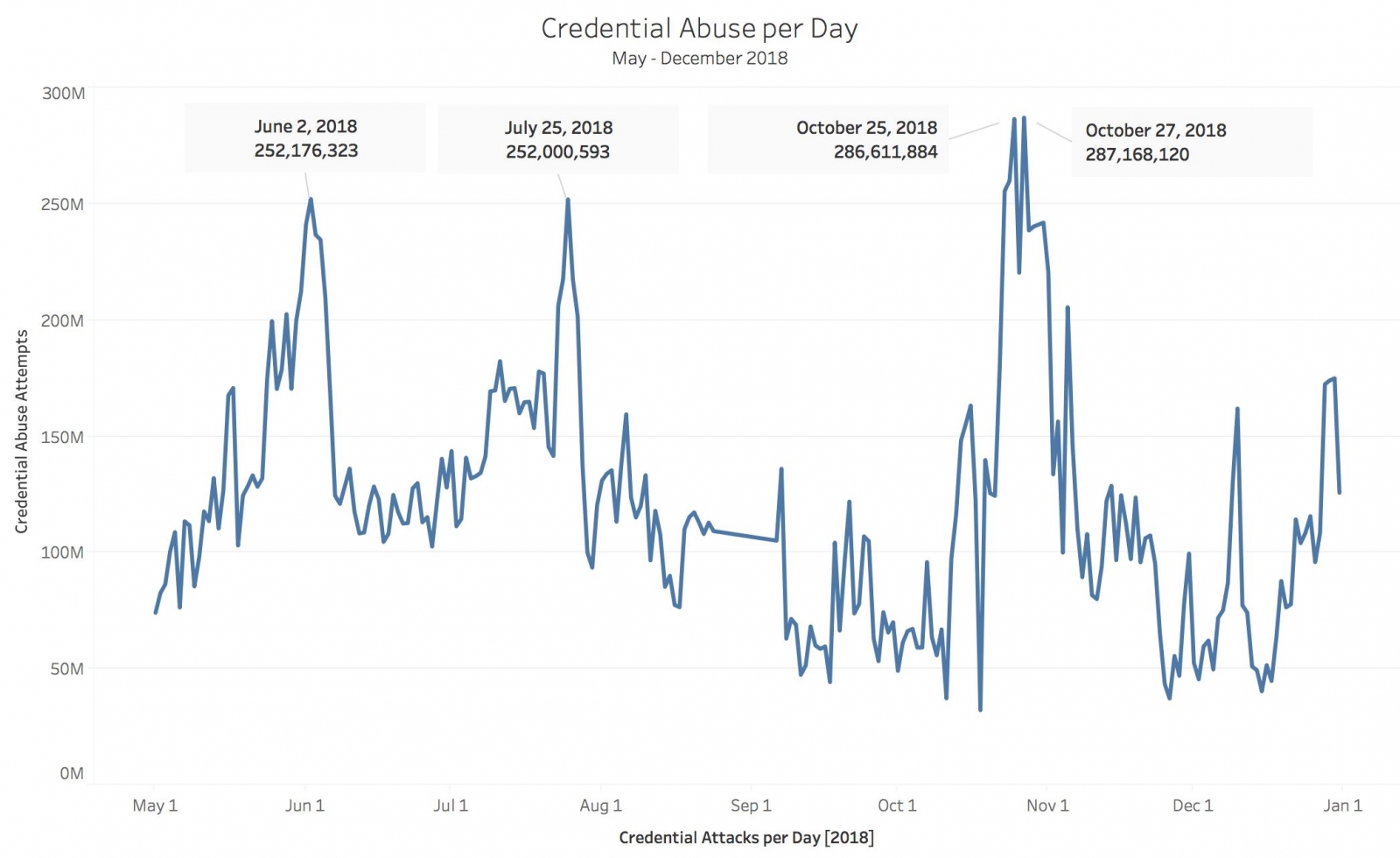
The Economy of Credential Stuffing Attacks
What Is Credential Stuffing?
How to Bypass Cloudflare in 2023: The 8 Best Methods - ZenRows
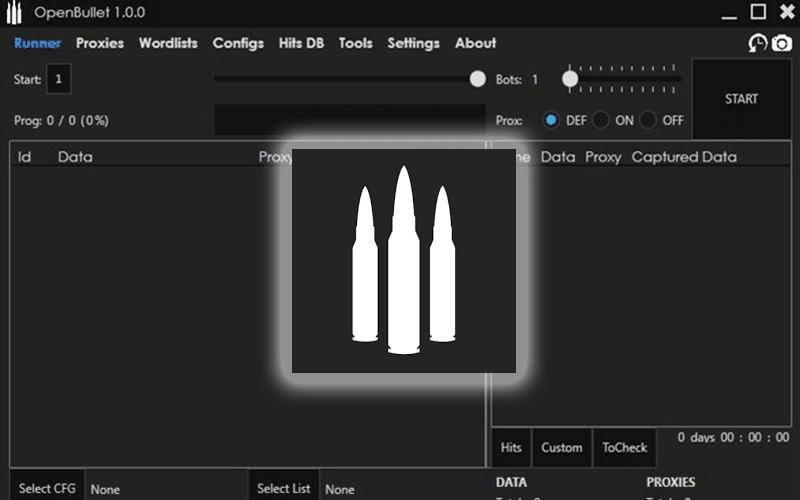
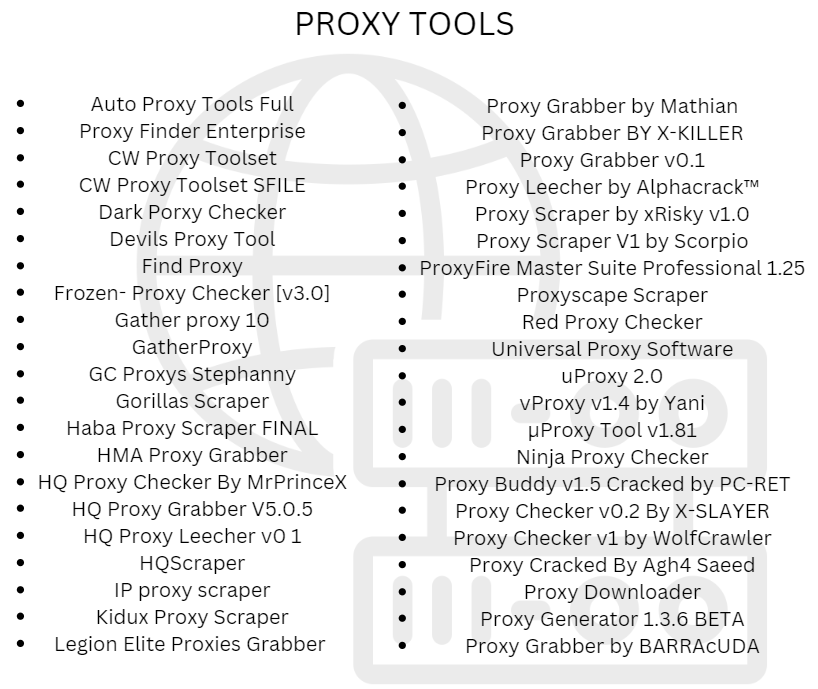
Cracking Tools that Automate Credential Stuffing & ATO

Best CAPTCHA Proxies in 2023 - ZenRows
Recomendado para você
-
Anti-Grabify09 novembro 2024
-
 How to Find Someone's IP Address on PS409 novembro 2024
How to Find Someone's IP Address on PS409 novembro 2024 -
 How to Get Someones IP from Steam Id09 novembro 2024
How to Get Someones IP from Steam Id09 novembro 2024 -
 Protect Yourself: Risks of Fake IPs, Free Proxies, and VPNs09 novembro 2024
Protect Yourself: Risks of Fake IPs, Free Proxies, and VPNs09 novembro 2024 -
Reverse IP Lookup #tools #free #unlimited #osint #reverse09 novembro 2024
-
Find the IP Address of my Website, Server and Domain09 novembro 2024
-
Can you obtain an IP address from a Facebook post? - Quora09 novembro 2024
-
![4 Ways in 2023] How to Find Someone's IP on Instagram?](https://images.imyfone.com/famiguarden/assets/article/monitor/ip-address-lookup.png) 4 Ways in 2023] How to Find Someone's IP on Instagram?09 novembro 2024
4 Ways in 2023] How to Find Someone's IP on Instagram?09 novembro 2024 -
Ps4 Ip Puller09 novembro 2024
-
 Comodo Dragon - Manage Extensions09 novembro 2024
Comodo Dragon - Manage Extensions09 novembro 2024
você pode gostar
-
 Superb Sonic Chaos remake for Windows by Hella from Hell. Free Indie remake for PC. Original by Sega in 1991. : r/IndieGaming09 novembro 2024
Superb Sonic Chaos remake for Windows by Hella from Hell. Free Indie remake for PC. Original by Sega in 1991. : r/IndieGaming09 novembro 2024 -
 Download do APK de Tile Onnect - Jogos de Combina para Android09 novembro 2024
Download do APK de Tile Onnect - Jogos de Combina para Android09 novembro 2024 -
 Assistir Mahoutsukai Reimeiki - Episódio 009 Online em HD - AnimesROLL09 novembro 2024
Assistir Mahoutsukai Reimeiki - Episódio 009 Online em HD - AnimesROLL09 novembro 2024 -
 Anime Darker Than Black 4k Ultra HD Wallpaper by RoninGFX09 novembro 2024
Anime Darker Than Black 4k Ultra HD Wallpaper by RoninGFX09 novembro 2024 -
 CR7 vai lançar um jogo de Futebol (UFL), Cr709 novembro 2024
CR7 vai lançar um jogo de Futebol (UFL), Cr709 novembro 2024 -
 ninho bebê com tranças para berço09 novembro 2024
ninho bebê com tranças para berço09 novembro 2024 -
 干货】马来西亚国民大学如何完成线上注册及选课? - 知乎09 novembro 2024
干货】马来西亚国民大学如何完成线上注册及选课? - 知乎09 novembro 2024 -
 Stream Battle for Humanity - Record of Ragnarok OST (Shuumatsu no valkyrie) (320 kbps).mp3 by Nashrullah Akmal Rabbani09 novembro 2024
Stream Battle for Humanity - Record of Ragnarok OST (Shuumatsu no valkyrie) (320 kbps).mp3 by Nashrullah Akmal Rabbani09 novembro 2024 -
 Papa's Pizzeria To Go! na App Store09 novembro 2024
Papa's Pizzeria To Go! na App Store09 novembro 2024 -
 Roblox Frontlines creator reveals how he made viral Call of Duty-inspired game - Dexerto09 novembro 2024
Roblox Frontlines creator reveals how he made viral Call of Duty-inspired game - Dexerto09 novembro 2024

