Windows Command-Line Obfuscation
Por um escritor misterioso
Last updated 10 novembro 2024
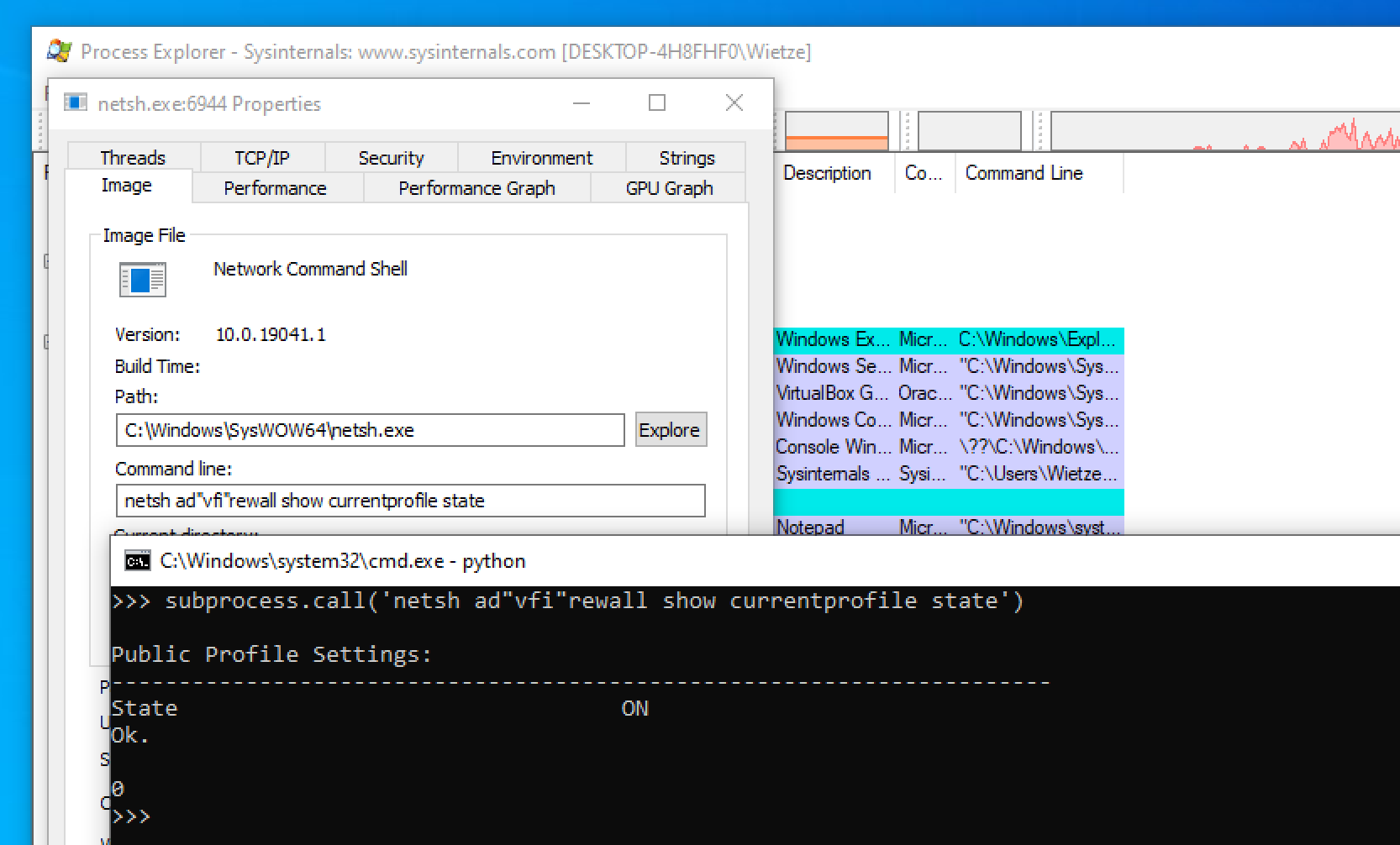
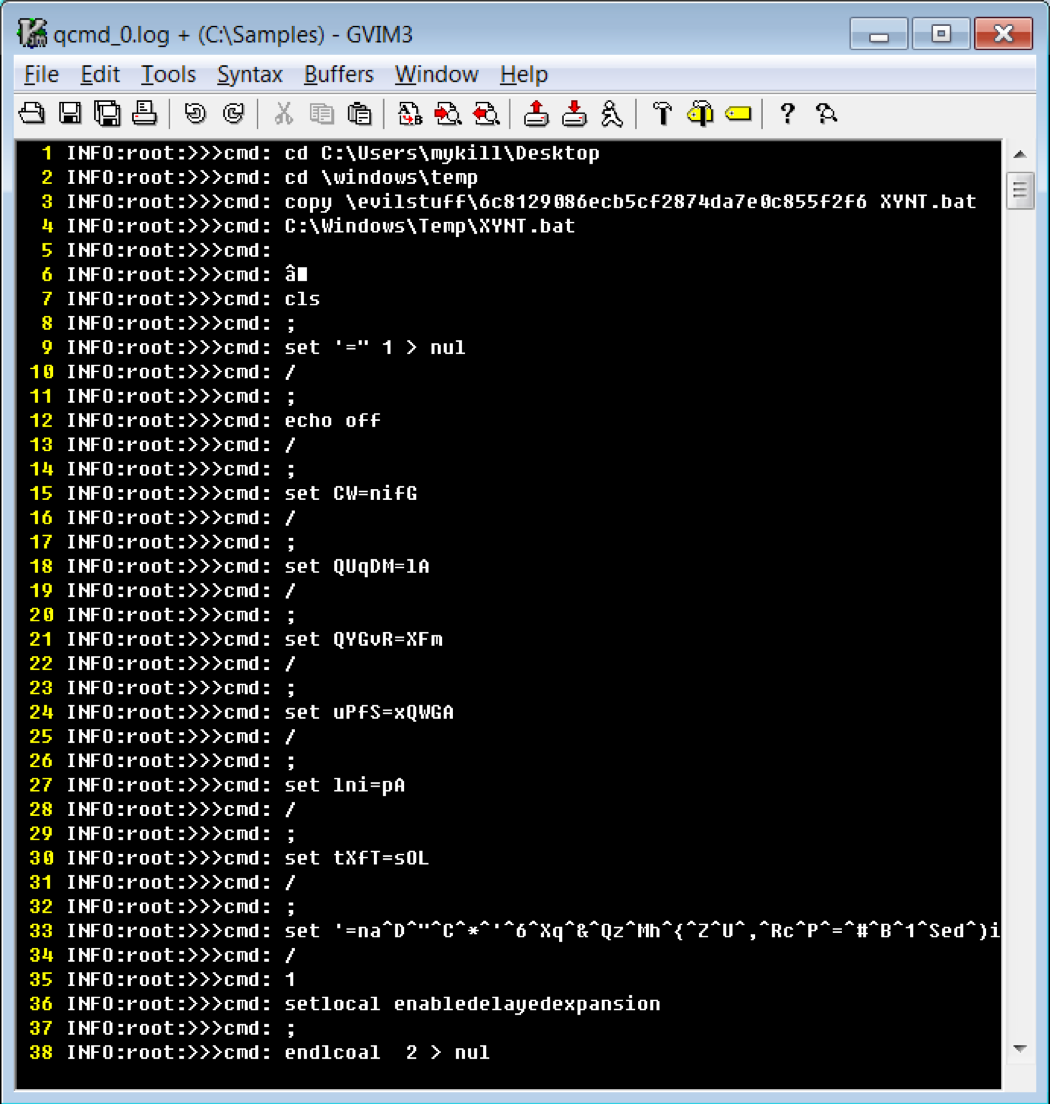
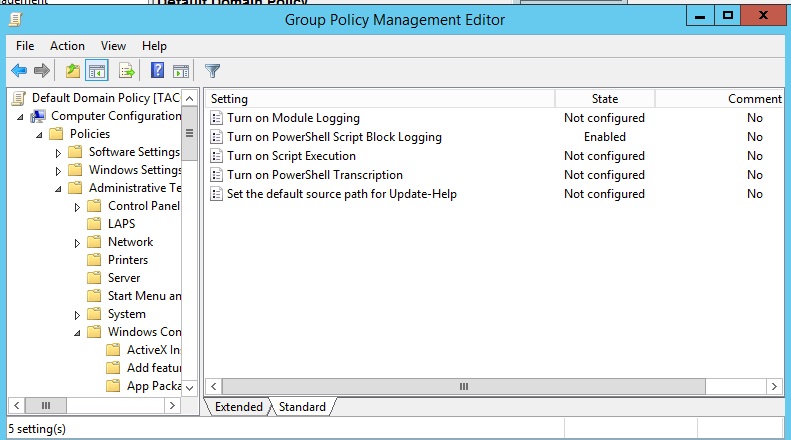
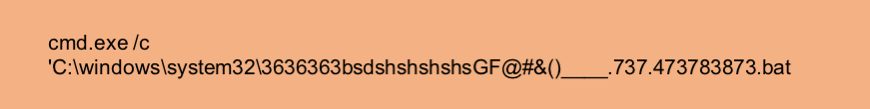
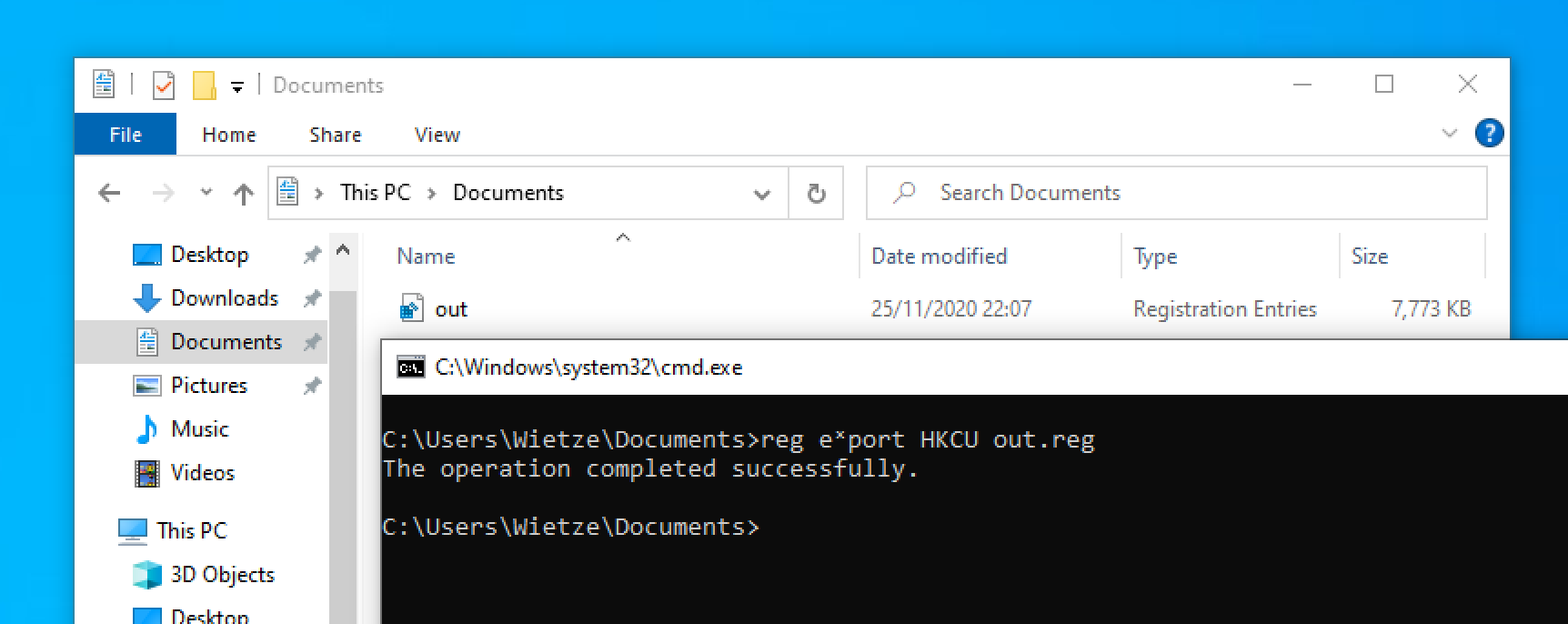
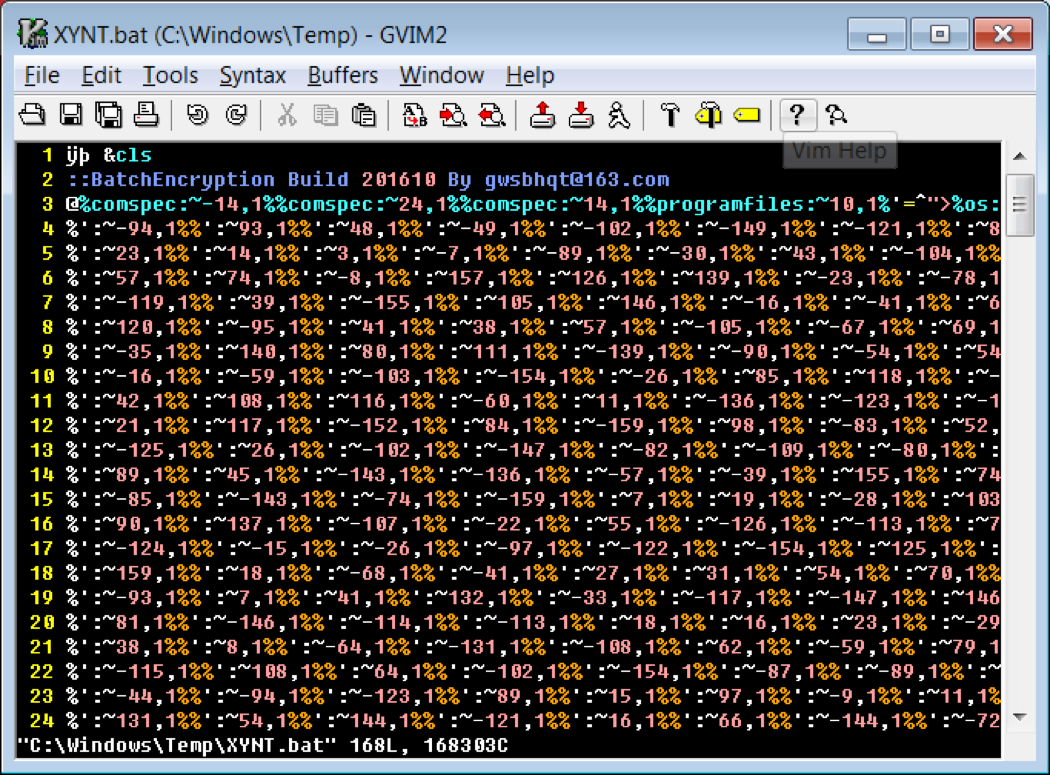
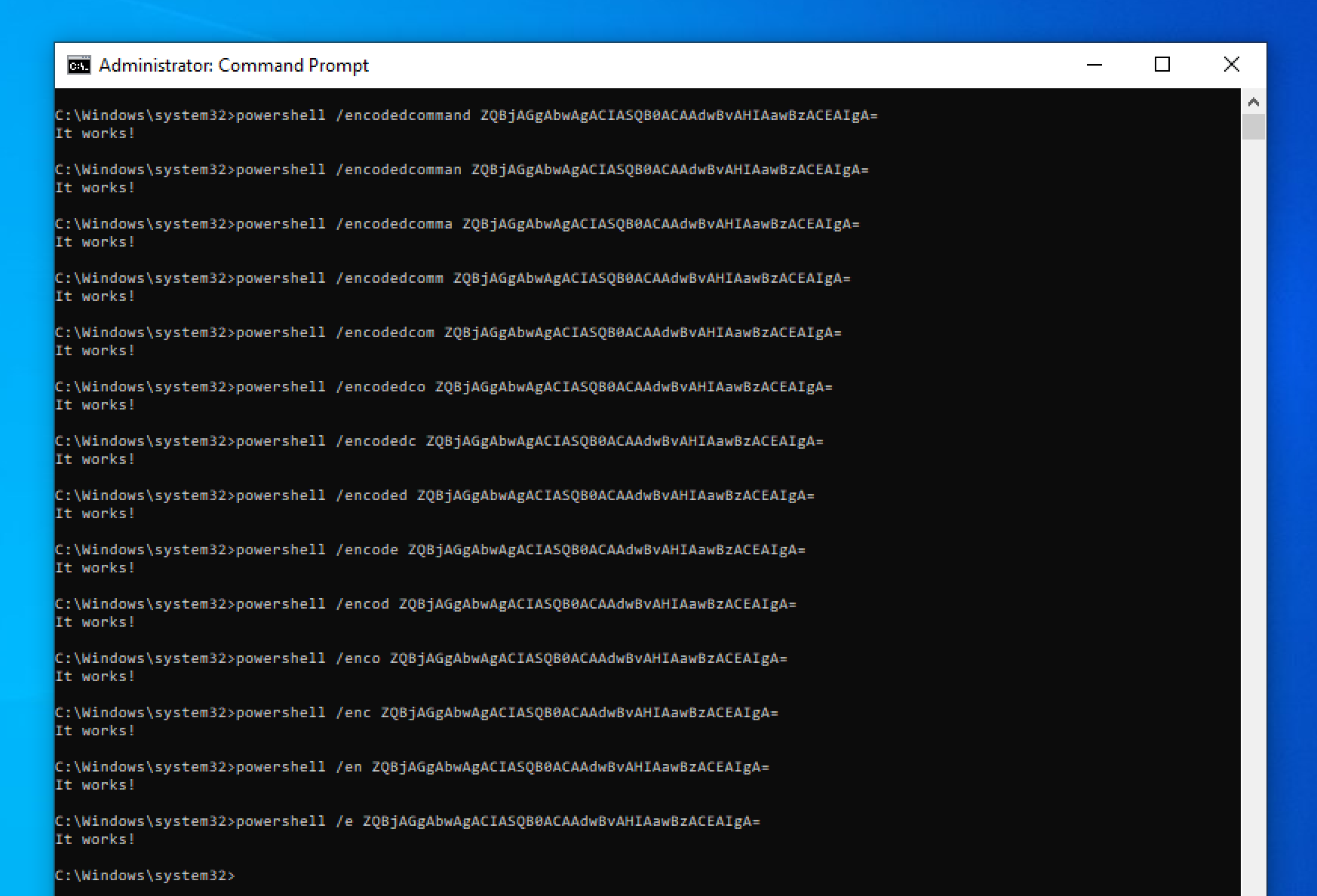
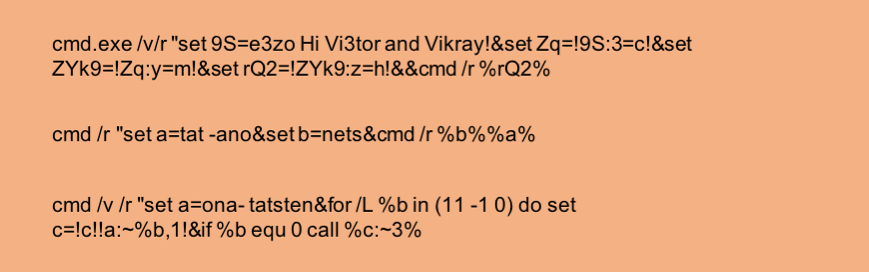
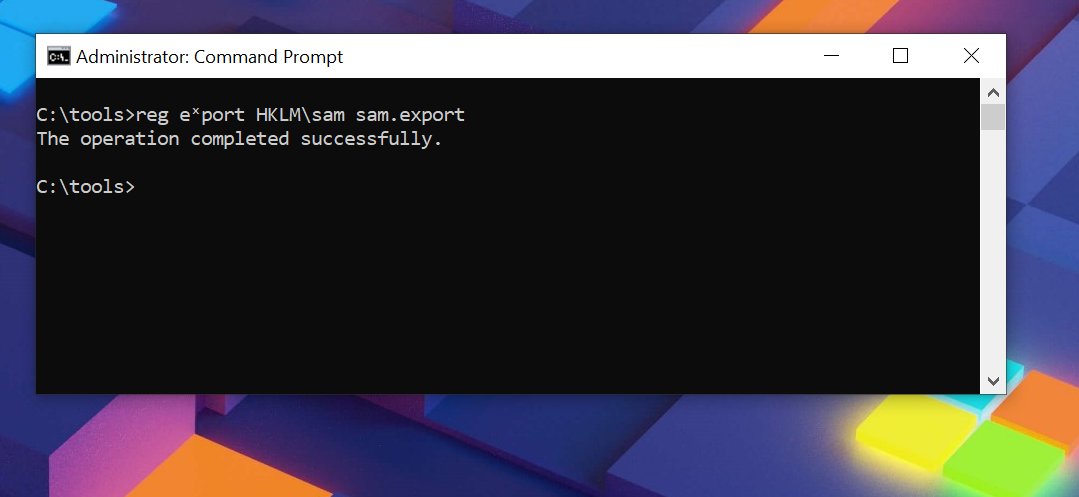
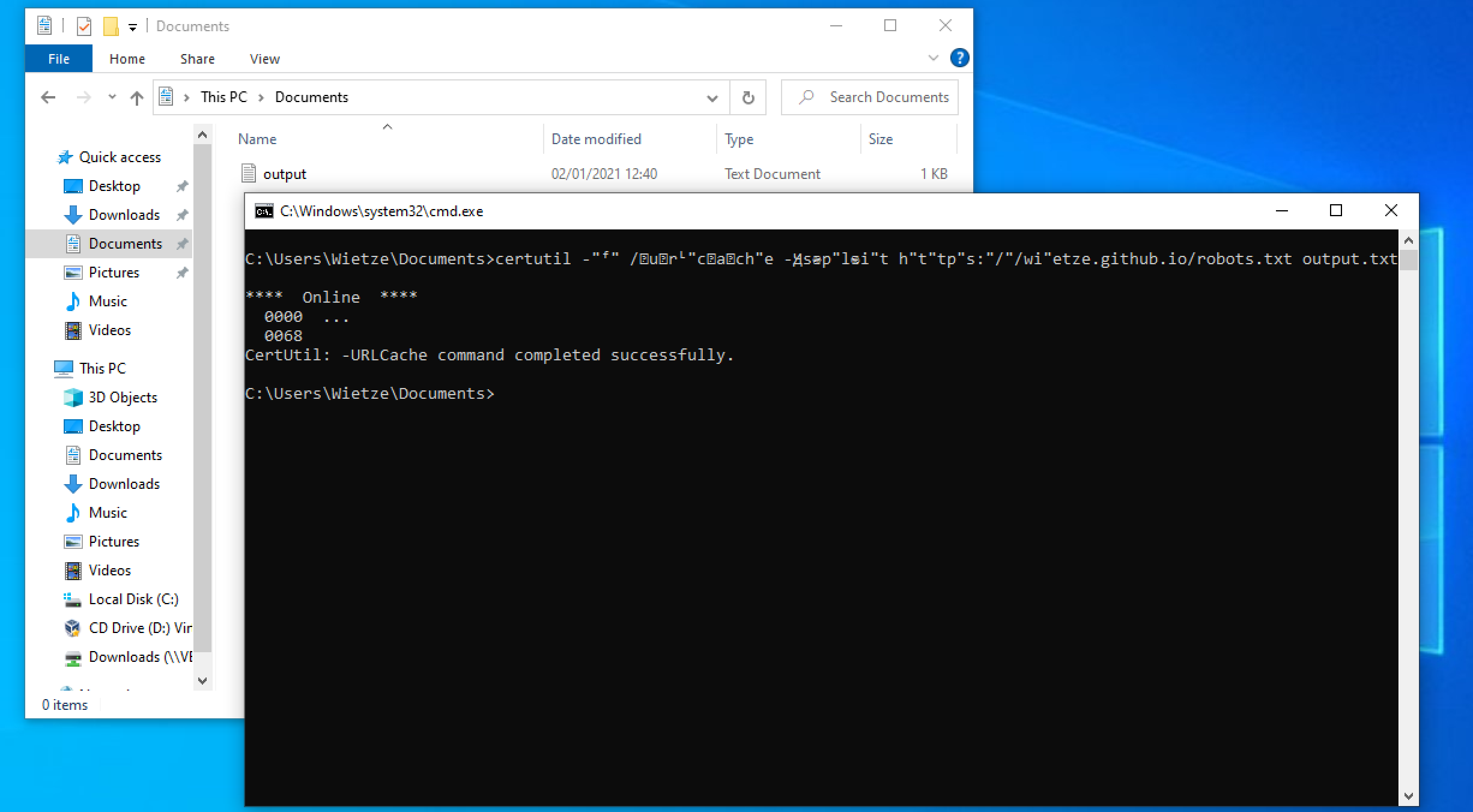
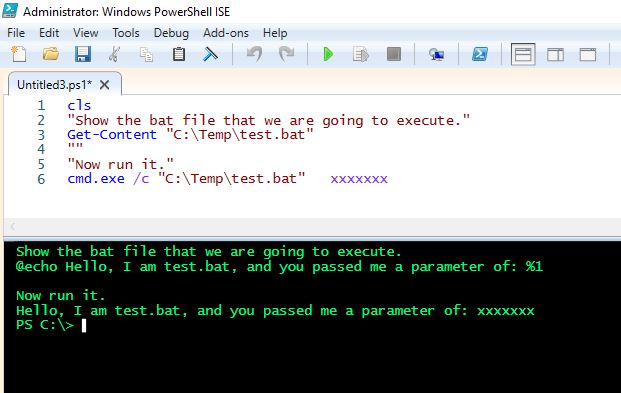
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.
Cmd and Conquer: De-DOSfuscation with flare-qdb - REAL security
PowerShell Obfuscation: Stealth Through Confusion, Part I

Tried and True Hacker Technique: DOS Obfuscation
Obfuscated Command Line Detection Using Machine Learning
Windows Command-Line Obfuscation
Cmd and Conquer: De-DOSfuscation with flare-qdb

Invoke-Obfuscation – Liam Cleary [MVP Alumni and MCT]
Windows Command-Line Obfuscation

Commandline Obfusaction - Red Team Notes
Obfuscated Command Line Detection Using Machine Learning
Florian Roth on X: Sigma rule to detect suspicious Unicode

AMSI Bypass Methods Pentest Laboratories
Windows Command-Line Obfuscation

Simple Obfuscation with PowerShell using Base64 Encoding
Recomendado para você
-
 Use PowerShell to execute an exe – 4sysops10 novembro 2024
Use PowerShell to execute an exe – 4sysops10 novembro 2024 -
 running a cmd within powershell - Microsoft Q&A10 novembro 2024
running a cmd within powershell - Microsoft Q&A10 novembro 2024 -
 Scheduling a PowerShell script… with arguments10 novembro 2024
Scheduling a PowerShell script… with arguments10 novembro 2024 -
 How to Get Silent Install parameters from a .exe10 novembro 2024
How to Get Silent Install parameters from a .exe10 novembro 2024 -
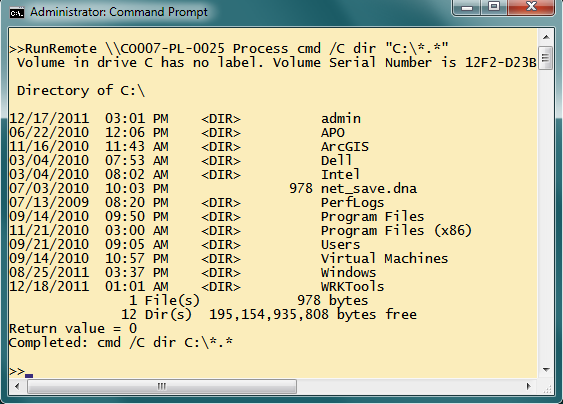 Running Any Command Line exe Remotely Using the Process Class10 novembro 2024
Running Any Command Line exe Remotely Using the Process Class10 novembro 2024 -
 windows - Applying a command line argument to the binary exe when10 novembro 2024
windows - Applying a command line argument to the binary exe when10 novembro 2024 -
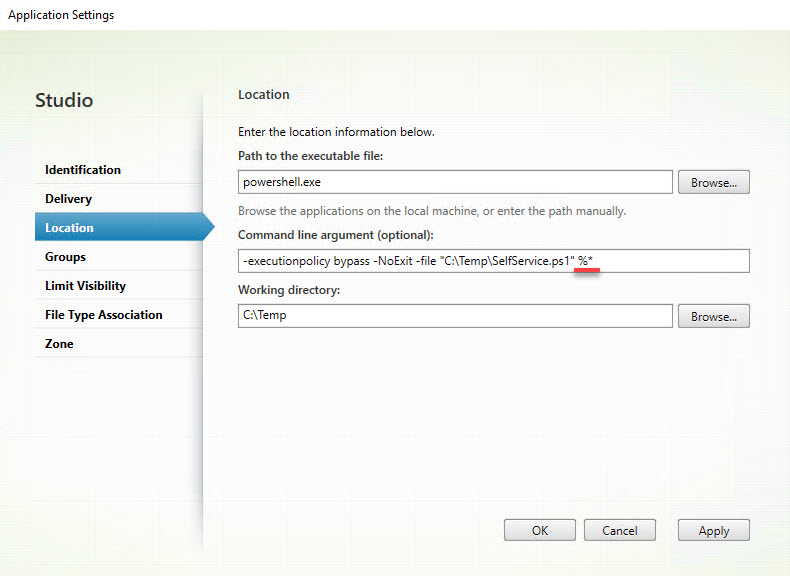 Parsing multiple parameters using the Citrix SelfService.exe10 novembro 2024
Parsing multiple parameters using the Citrix SelfService.exe10 novembro 2024 -
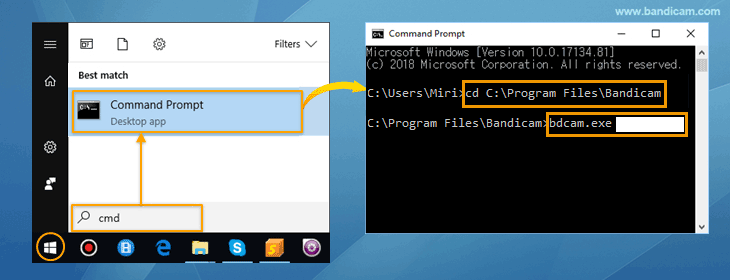 Command-Line Parameters - Bandicam Screen Recorder10 novembro 2024
Command-Line Parameters - Bandicam Screen Recorder10 novembro 2024 -
 Question execution of setup in silent mode - General Discussion10 novembro 2024
Question execution of setup in silent mode - General Discussion10 novembro 2024 -
 Client User Interface > Main menu > Server > Jobs - Jobs > Job10 novembro 2024
Client User Interface > Main menu > Server > Jobs - Jobs > Job10 novembro 2024
você pode gostar
-
 Becky Lynch defeats Tiffany Stratton for WWE NXT Women's Championship - WON/F4W - WWE news, Pro Wrestling News, WWE Results, AEW News, AEW results10 novembro 2024
Becky Lynch defeats Tiffany Stratton for WWE NXT Women's Championship - WON/F4W - WWE news, Pro Wrestling News, WWE Results, AEW News, AEW results10 novembro 2024 -
 tenis Mad Rats Slip On Quadriculado10 novembro 2024
tenis Mad Rats Slip On Quadriculado10 novembro 2024 -
 Super Mario Bros. (1993)10 novembro 2024
Super Mario Bros. (1993)10 novembro 2024 -
 Relembre as máximas filosóficas em Youkoso Jitsuryoku Shijou no10 novembro 2024
Relembre as máximas filosóficas em Youkoso Jitsuryoku Shijou no10 novembro 2024 -
 National Geographic ™ S.T.E.M. Gold Doubloon Dig Kit10 novembro 2024
National Geographic ™ S.T.E.M. Gold Doubloon Dig Kit10 novembro 2024 -
 Venge.io by commention10 novembro 2024
Venge.io by commention10 novembro 2024 -
Sarada Uchiha wallpaper by IsaacMenezesSoares - Download on ZEDGE10 novembro 2024
-
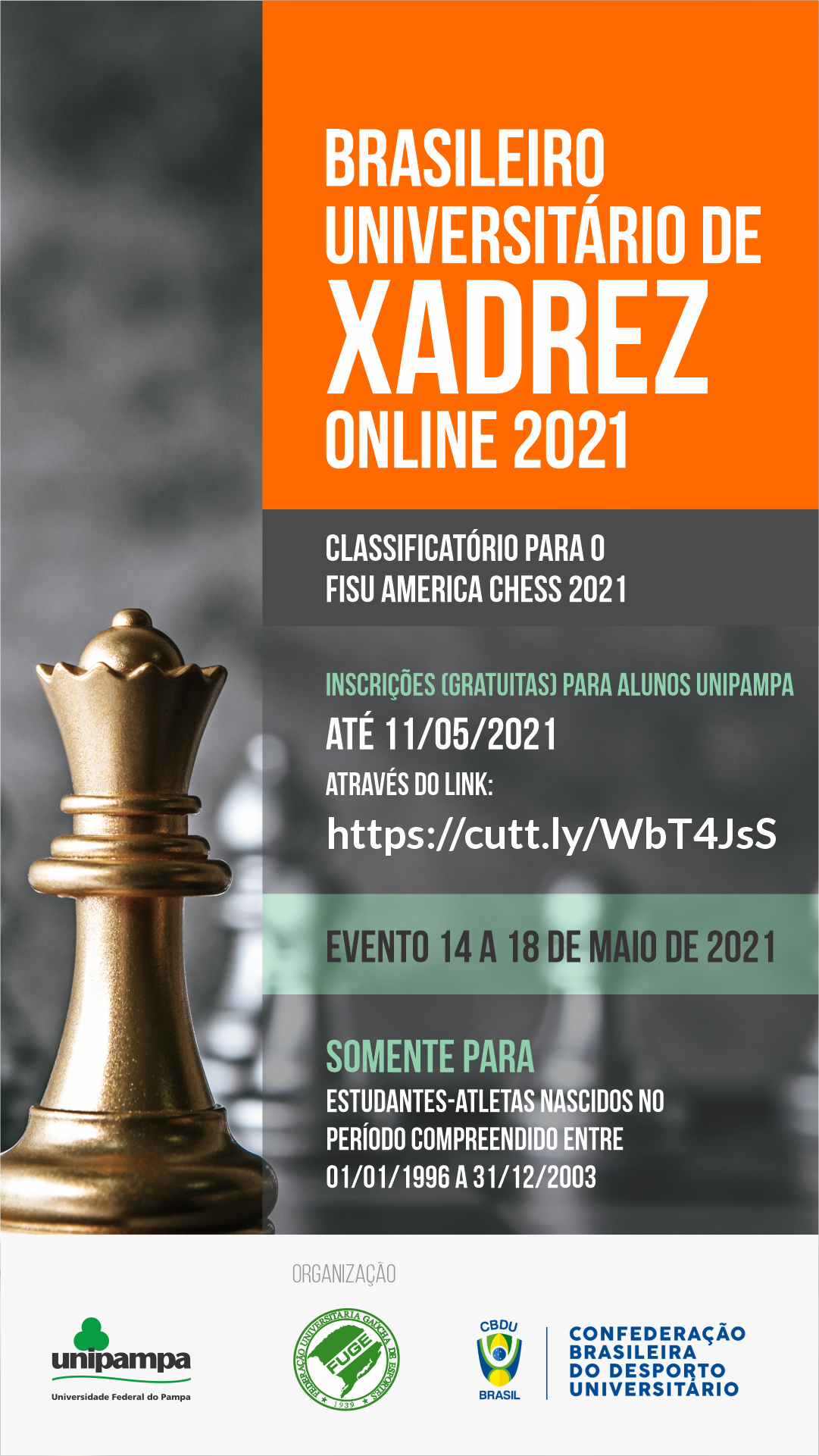 Unipampa recebe inscrições para o Brasileiro Universitário de10 novembro 2024
Unipampa recebe inscrições para o Brasileiro Universitário de10 novembro 2024 -
 How To Evaluate Your Event Effectively: A Step-by-Step Guide From10 novembro 2024
How To Evaluate Your Event Effectively: A Step-by-Step Guide From10 novembro 2024 -
 Onde estão os jogadores que formaram a seleção do Brasileirão10 novembro 2024
Onde estão os jogadores que formaram a seleção do Brasileirão10 novembro 2024